What Is Blockchain Security?
Blockchain security is a mix of tools and procedures that protect your blockchain-based system and its users from external and internal threats. The list of protections includes anything from smart contract auditing and penetration testing to employee training and contingency planning. It’s necessary to implement several forms of blockchain security as no single system is perfect, and malicious parties are continuously improving their tactics.
Here, we break down a simple list of blockchain security practices and why they’re critical for any reputable business.
Penetration Testing
Penetration testing is probably the main activity you think of when you hear blockchain security. The purpose of a penetration test, or pen test for short, is to simulate an attack on your blockchain system, exposing both its vulnerabilities and its strengths.
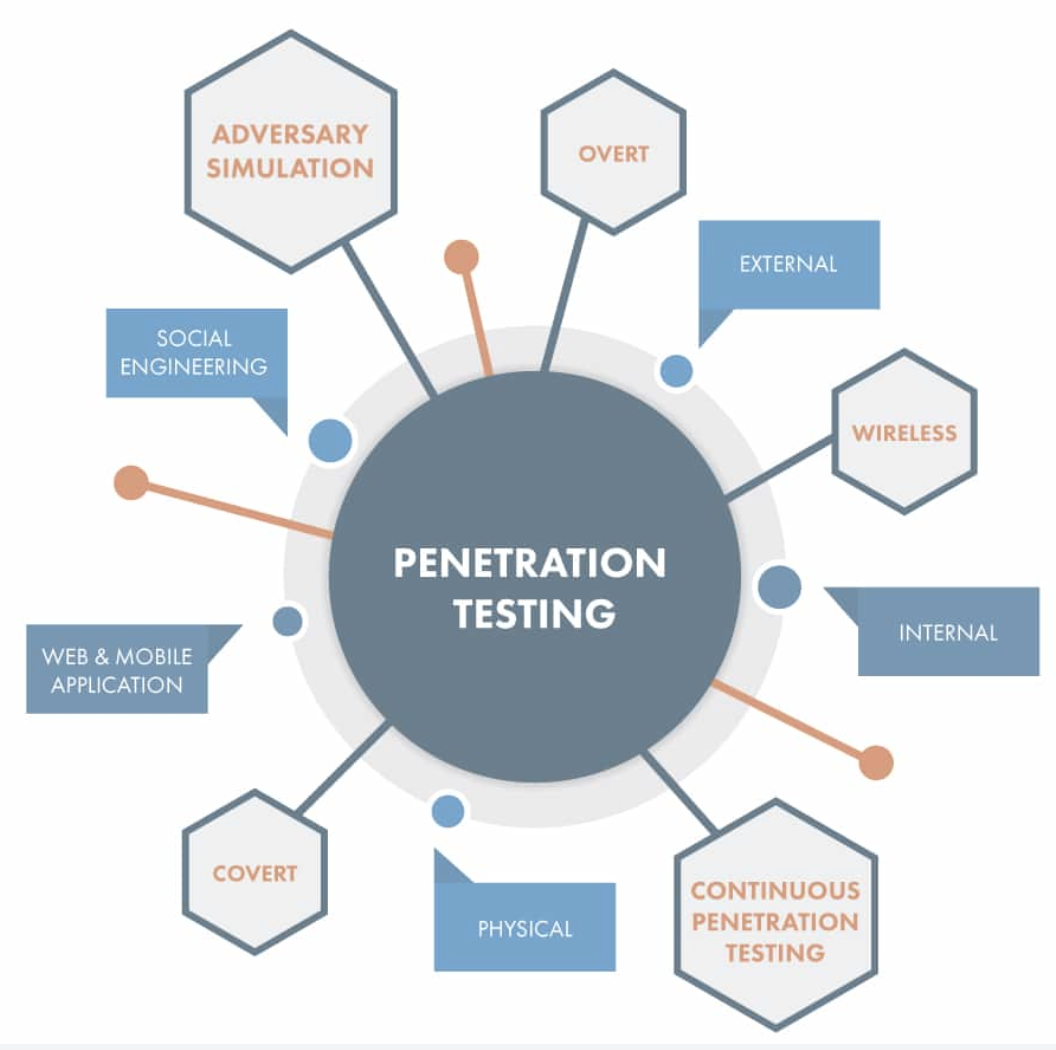 Penetration testing involves much more than testing code. | Source: ICSS
Penetration testing involves much more than testing code. | Source: ICSS
Beyond software security tests, you can use penetration testing to analyze your company’s regulatory compliance (or lack of it), measure employee security engagement, and determine the responsiveness of your business to different types of blockchain security threats.
Code Reviews, Quality Assurance, and Smart Contract Auditing
These practices technically fall under the penetration testing umbrella, but they’re so vital that we felt it necessary to give them a section to themselves.
At their core, blockchain systems are just software, and as every seasoned software developer knows, even the most well-written program has bugs. It’s crucial that you get multiple sets of eyes on your blockchain’s code as early as possible.
Blockchains are significantly more challenging to update than other types of software infrastructure. Depending on your blockchain’s architecture and consensus mechanism, any change may require a hard fork or cause a split into two, distinct chains.
If your team is large enough, incorporate code reviews, in which programmers review the work of their peers before committing changes, into your development process. You should also implement quality assurance practices, such as automated, manual, and different forms of load testing. You may even consider test-driven development for additional code coverage.
 A simple way to add code reviews to your development process. | Source: Atlassian
A simple way to add code reviews to your development process. | Source: Atlassian
Auditing your smart contracts is a must. You should not only do this internally but also splurge for a third-party security firm to dig in as well. There are plenty of hackers waiting for the opportunity to take advantage of poorly written smart contracts, so a relatively small payment now could save you millions of dollars down the road.
Password and Key Management
A common vulnerability of blockchain-based companies is in their storage of passwords, private keys, and other essential information. There are two main threats regarding these things which you should be aware of – loss and theft.
It’s near impossible to recover a private key if you’ve lost it. These complex strings are usually your last line of defense in accessing your cryptocurrency wallets, so if you misplace them, you’re out of luck. Blockchain doesn’t have a forgot password option.
Knowing a company’s passwords or private keys effectively permits you free access to any of the associated accounts. So it’s no wonder that this information is such a hot target for criminals. Thieves use a variety of tactics (malware, phishing, social engineering, hacks, black market deals, you name it) to get ahold of your credentials.
When creating passwords, ensure that they are substantially lengthy and use a mixture of capital letters, lowercase letters, numbers, and special characters. Never use the same password twice. If you have trouble remembering a multitude of secure passwords (don’t worry, most people do), try out a reputable password manager such as LastPass.
Although you need to store both securely, you should treat private keys differently than passwords. Encrypt your private keys if you’re storing them on your computer. Even better, keep them somewhere offline. It’s not unheard of to write them down and securely store them in one, or several, safety deposit boxes.
It’s also wise to hold multiple copies of your private keys in separate locations to ensure you still have them in the event of an unforeseen catastrophe.
Contingency Planning
Every blockchain enterprise has security flaws; they’re inevitable. While the occasional security mess-up is forgivable, the failure to have a contingency plan when it does is reprehensible.
A well-thought-out contingency plan includes a list of your top blockchain security risks and scenarios if they occur. After performing your penetration tests, creating this list should be a breeze.
You need to publish meticulously detailed documents on what to do in the event of each blockchain security breach, including several layers of contingency across numerous different scenarios, to the entire company. Make sure that every employee knows how to access the documents. You don’t want anyone to have any questions once disaster strikes.
Employee Training
Speaking of employees, learning and getting familiar with your company’s blockchain security policies needs to be part of every employee’s onboarding.
Other than that, you should have regularly scheduled security meetings to discuss any new security threat findings and provide a retrospective on previous slip-ups. You may consider company-wide testing every once in a while as well to keep employees’ blockchain security knowledge fresh.
End-User Protection
You could have all the internal protections in the world and still run into security issues from end-users who don’t have the knowledge base they need to operate your application safely.
Lost or stolen keys, phishing attempts, malware – they don’t just threaten your business; they threaten your customers as well. And when customers become victims, they often place blame on the company, even if you’re not at fault.
From a security standpoint, it’s best for end-users to be the only party with access to their keys and passwords. However, limiting this access could cause a poor user experience. If a customer loses their private key, for instance, they’re out of options and can no longer access their wallet.
Consider implementing a key management system to help your users recover lost keys and passwords. When it comes to password and key storage, some people simply trust a company more than they trust themselves.
It’s imperative to inform your users about potential security threats. The cryptocurrency industry is rife with scam artists and criminals ready to pounce on unsuspecting victims. So the best way to protect your users is through education.
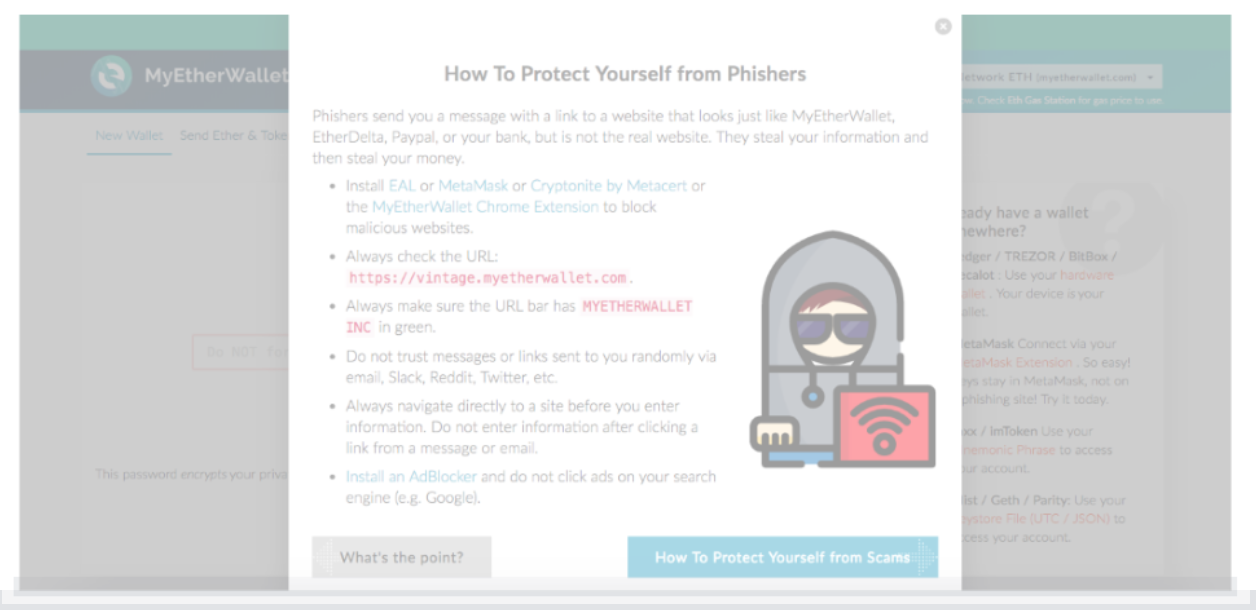 MyEtherWallet ensures that their users know about common phishing threats. | Source: MyEtherWallet
MyEtherWallet ensures that their users know about common phishing threats. | Source: MyEtherWallet
Educate your end-users on the different tactics of phishers. Give them examples of copycat websites and phony links. And, if you discover a potential security threat, let your customers know immediately.
Equally as important, provide your customers with tools to help boost their security. Security-conscious companies create incentives for activities that improve individual defenses, like enabling two-factor authentication. The less your customers see personal protection as a burden, the better off them and your business are.
Why Is Blockchain Security Important?
Because the survival of your business depends on it, literally. One security breach and you could lose the trust of your customers forever. A small mistake and the funds in your company’s crypto wallet are instantly cleaned out.
Take blockchain security seriously. Start building your blockchain security plan today.

