Data From 200 US Police Departments & Fusion Centers Published Online
296GB of data has been stolen from US law enforcement agencies and fusion centers by an activist group named Distributed Denial of Secrets(DDoSecrets) and put online into a searchable portal. According to ZDNet, the portal contains more than one million files including audio files, videos, emails, and more.

ZDNet
DDoSecrets has stated the files included in the data dump date back ten years and belong to over 200 police departments and other law enforcement training and supportive services.
“Ten years of data from over 200 police departments, fusion centers and other law enforcement training and support resources. Among the hundreds of thousands of documents are police and FBI reports, bulletins, guides and more.https://t.co/sWzdKc2VFc”
The data published has supposedly originated from a web development organization called Netsential. KrebsOnSecurity supported this statement, affirming “that the National Fusion Center Association (NFCA), the central association representing all fusion centers across the US, confirmed the leak’s authenticity in an internal security alert it sent to its members.”
The leak quickly gained attention using the #blueleaks hashtag throughout Twitter and other social media. Analysis of the documents revealed that the FBI has monitored the social accounts of protesters who uttered anti-police messages and sent alerts to police stations and Bitcoin donations to protest groups are constantly being tracked.
Read more here.
Akamai mitigated the ‘largest’ ever PPS DDoS attack
On June 21, 2020, the largest ever PPS DDoS attack which reached a record 809 million packets per second (PPS) was mitigated by Akamai, an intelligent cloud computing platform. The attack was geared towards an unnamed bank and totaled up to 418Gbps. Typical DDoS attacks are measured in bits per second (bps), unlike PPS-focused DDoS attacks, which aim to overwhelm the resources within a network’s gear in a customer’s data center/cloud environment. Vs the capability of the circuits.
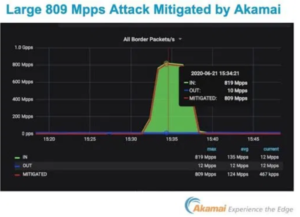
According to Akamai’s report, “The attack grew from normal traffic levels to 418 Gbps in seconds, before reaching its peak size of 809 Mpps in approximately two minutes. In total, the attack lasted slightly less than 10 minutes.”
Additionally, 96.2% of the IP addresses involved in the attacks were seen for the first time by the organization and was determined to have been optimized to overwhelm the DDoS mitigation systems put into place.
Amazon’s AWS shield has recently announced that they mitigated the largest DDoS attack, a 2.3 Tbps attack, which overtook the previous record of 1.7Tbpts that took place in March 2018.
Read more here
Nvidia Warns Windows Gamers of Serious Graphics Driver Bugs
Nvidia, a graphics chipmaker has fixed two high-severity flaws in its graphics drivers. These flaws, if exploited, can allow an attacker to gain elevated privileges on the system, launch denial-of-service attacks, or view sensitive data. One vulnerability (CVE‑2020‑5963) exists in the CUDA driver, which stems from improper access in the driver’s IPC API’s. The other vulnerability, CVE-2020-5962, exists in the Nvidia Control Panel component, which provides access to graphic driver settings. Other vulnerabilities could lead to code execution DOS or information disclosure.
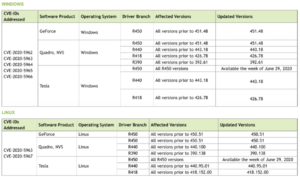 Nvidia has released several patches fixing high-security vulnerabilities within the past few months, several of which could be exploited by an attacker to launch DoS or code-execution attacks.
Nvidia has released several patches fixing high-security vulnerabilities within the past few months, several of which could be exploited by an attacker to launch DoS or code-execution attacks.
Read more here.
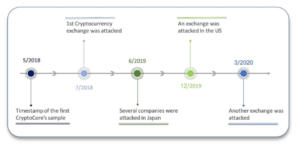
CryptoCore Hackers Made Over $200M Breaching Crypto Exchanges
According to a new report by ClearSky, a hacking group dubbed Crypto Core has targeted cryptocurrency exchanges with spear-phishing attacks to successfully infiltrate and steal over $200 million since 2018.
The group initially goes through an extensive reconnaissance phase to discover specific, valuable, targets (personal email accounts, employee background information, and more). Once this is completed, the spear-phishing attacks then utilize custom domains, and impersonation methods to impersonate executives, mimic affiliated companies, and more.

When a victim downloads the malicious documents within the email, they are provided with a protected file that requires a password to open them. The password is located in the Password.txt.lmk file, which when opened downloads other malicious files.
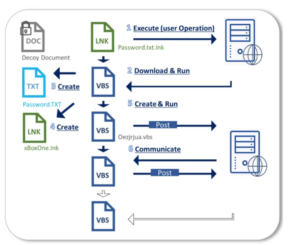
Clearsky
Once the host is infected, the CryptoCore group utilizes various payloads to steal crypto-wallet keys that are typically stored in password managers. Other areas of attacks include utilizing Mimikatz to conduct lateral movement and search for additional user keys.
CryptoCore has tended to target companies in the United States and Japan, their origins have links to Ukraine, Russia, and East European Countries; however, the true location is not entirely known.
Read more here.
Microsoft Defender ATP Now Scans Windows 10 PC Firmware for Hardware Rootkit Attacks
Several firmware-level defenses that have been incorporated into Windows 10 Secured-Core PCs are now being implemented into its enterprise antivirus software, Microsoft Defender Advanced Threat Protection (ATP). Protections include kernel Direct Memory Access (DMA) protection, Trusted Platform Module (TPM), and Unified Extensible Firmware Interface (UEFI) scanner.
DMA protection mitigates hands-on attacks that can be used to exploit and then steal data from memory (Thunderbolt attack). TPM, combined with hypervisor-protected code integrity is utilized to block unverified code execution.
The new UEFI scanner in Windows Defender ATP is used to scan the sector between the operating system and firmware. This feature provides an additional level of protection by detecting rootkits or other malware attacks where the secure boot is disabled or the motherboards chipset is misconfigured.
Microsoft Defender has received a large amount of support in the past year and has expanded its services to Linux and Android devices.
Read more here.

