
As the adage goes, “A fool in his money are soon parted.” Whether it’s by your own doing, like throwing away an old hard drive, or someone else’s, there’s no shortage of ways to part with your crypto. Here, we break down the top nine ways to lose your cryptocurrency so that you can learn from the mistakes of those before you.
1. Lose Your Private Key
Arguably the most foolish way to lose your cryptocurrency is by misplacing your private key. Without this complex string of characters, you have no way of accessing your cryptocurrency funds. You use your private key to sign transactions, so without it, you’re unable to send anything from your wallet.
You should have a redundant number of private key copies. Export your keys to a file, print them as a paper wallet, write them down, use a mnemonic seed phrase – whatever it takes to ensure that you won’t lose or forget them. Once it’s lost, no one can recover it. It’s not like a safe that a locksmith can open.
2. Store Critical Information Unencrypted
Assume that any malicious party has access to the information you leave unencrypted on your computer. Hackers stole over $2 million from Ian Balina, a well-known crypto trader, after noticing that he kept plaintext versions of his private keys on Evernote.
You need to encrypt and password-protect any critical information, such as private keys and passphrases, that you store on your computer. For an additional layer of security, encrypt your emails and whatever other communication channels you can as well.
Your computer is an attack vector. It’s relatively simple for a hacker to gain access to the information you store on it through malware or even a keyboard logger. So, an even better strategy is to not store critical information on your computer at all.
It’s best practice to write down your seed phrases using good ol’ pen and paper. Many security-minded folks store those pieces of paper in safety deposit boxes for additional protection. Some even take it a step further by separating phrases into parts and placing them in several different safety deposit boxes.
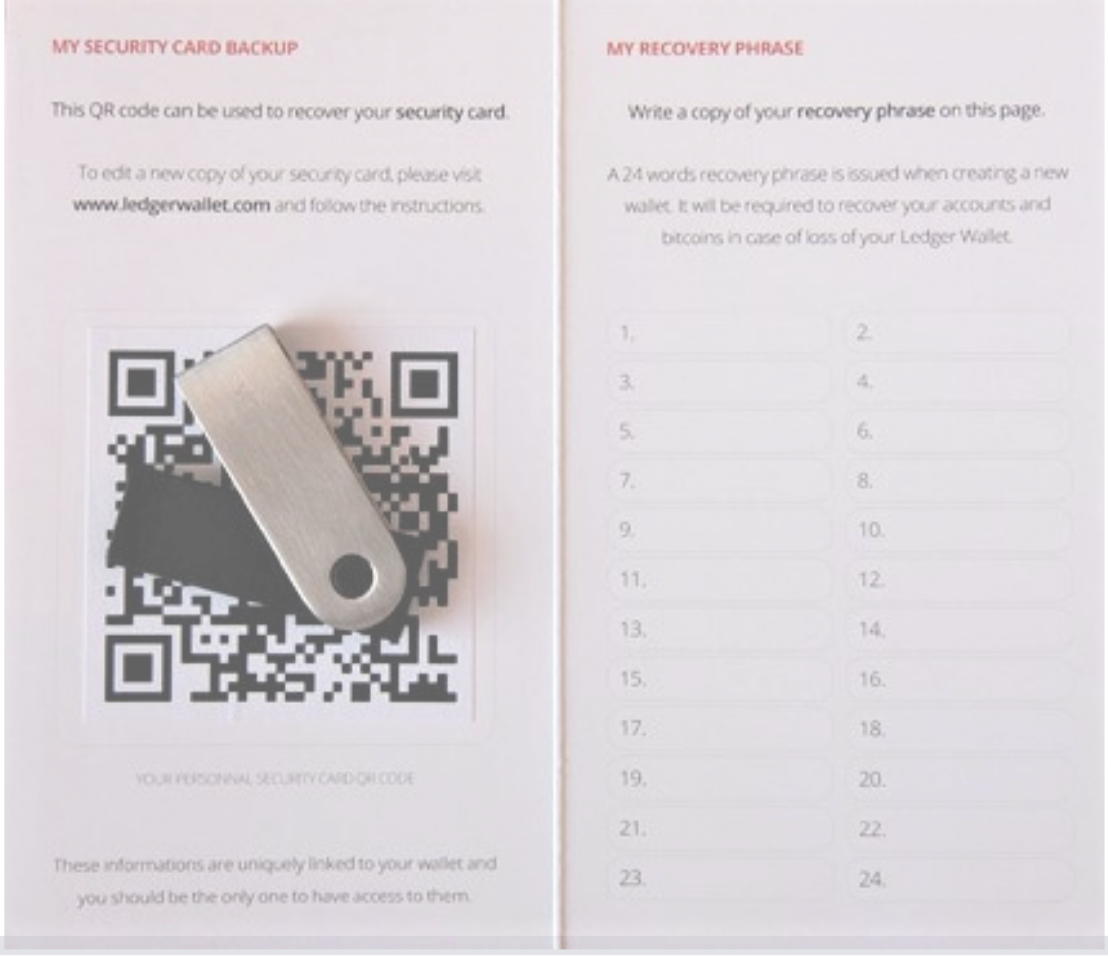 Ledger provides you with a handy notecard to store your seed phrase. | Source: Bitcoin Best Buy
Ledger provides you with a handy notecard to store your seed phrase. | Source: Bitcoin Best Buy
3. Keep Your Crypto on an Exchange
If the recent $40 million Binance hack teaches us anything, it’s that no exchange, no matter how trustworthy, is safe from hackers. Although Binance is recouping victim’s losses from its SAFU fund, not all exchange platforms are so generous. Victims of the 2014 Mt. Gox hack are still waiting on payouts.
— Binance (@binance) May 8, 2019
Because of their centralized structure and the massive amount of funds they hold, exchanges are a frequent hacking target. Keep as little cryptocurrency on trading platforms as you can. Instead, secure your cryptocurrency with a hardware wallet in which you hold the keys, not an exchange.
4. Use a Weak Password or Reusing Passwords
Weak passwords aren’t just words or phrases that are easy to guess. If you have a complex password but use it for multiple accounts, you’re following poor security practices. A breach on one of those platforms could potentially affect every account with which you use that password.
 These stats are from 2014. A hacker could crack your password in even less time today.
These stats are from 2014. A hacker could crack your password in even less time today.
Don’t re-use passwords, and ensure that each of yours includes a mix of uppercase and lowercase letters, numbers, and symbols. Beyond complexity, it’s critical that your passwords have a significant length to deter brute force attacks. Hackers can crack a password with just eight characters in less than two and a half hours.
5. Don’t Use Two-Factor Authentication (2FA)
Two-factor authentication is critical for any important crypto function. Without 2FA, a criminal could access your account with only your username and password. Companies suffer data breaches all the time, so this information is more readily available than you would think.
If you have 2FA enabled, a hacker needs access to your phone, email account, or yourself physically to gain access. Most cryptocurrency platforms support 2FA although they differ in the type they implement. Some use SMS and email; others integrate authentication apps like Authy or Google Authenticator. A few companies utilize biometrics.
You should enable 2FA on as many business functions as you can. Logging in, moving funds, making trades – 2FA for all of them. Stay vigilant even after implementing 2FA as criminals use tactics like SIM swapping to bypass 2FA security measures.
6. Fall Victim to Phishing
Phishing scams are one of the most common methods for criminals to obtain login credentials and private keys. Often, phishers will contact you pretending to be an authority in the space like an exchange, dApp, or wallet provider. They’ll copy everything from the official branding to the website URL and pressure you into sending your account credentials. Once they have those, they clear everything out.
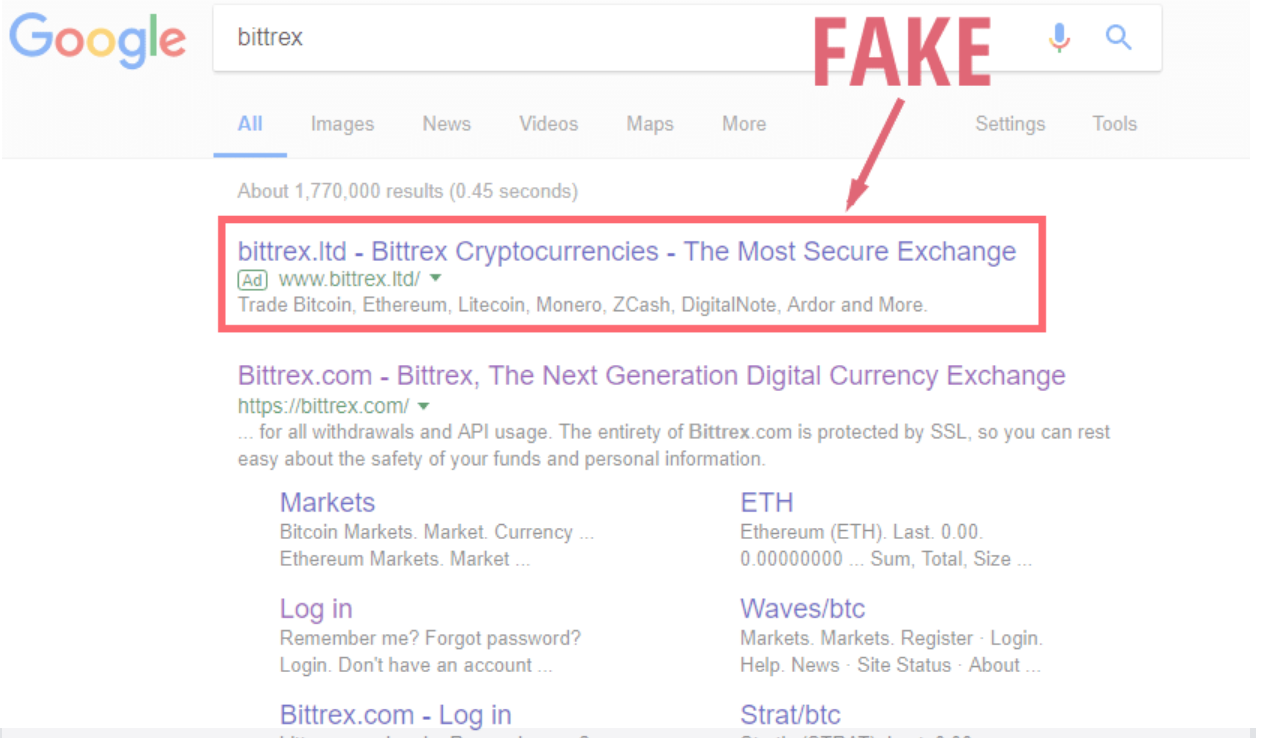 Phishers will sometimes buy Google ad space pretending to be a reputable company. | Source: Ethereum World News
Phishers will sometimes buy Google ad space pretending to be a reputable company. | Source: Ethereum World News
There are a few things to remember to avoid falling for a phishing scam:
-
Always type in URLs directly into your address bar
-
Don’t click on suspicious links.
-
Don’t upload your private keys to any site. Even trusted sites could get breached.
-
Additionally, fact-check information across multiple communication channels.
Finally, if an offer sounds too good to be true, it probably is.
7. Hand Over Your API Keys
Whenever you give your API keys to a third-party, you run the risk of them doing something malicious with your account. Trading bots and other cloud-based services commonly access a user’s API keys to perform trades on their behalf. Even if withdrawals are disabled, you should be hesitant to give your API keys out to anyone.
In 2018, several Binance customers were using a third-party trading bot that began placing orders without their permission to pump the price of Viacoin. Because the Viacoin price was artificially inflated, the victims were losing a significant amount of money on the trades. Binance was able to freeze the accounts and reverse the trades, but situations rarely play out like that for the victims.
8. Download Malware
Malware can take your cryptocurrency using a whole host of techniques. One example, CookieMiner, steals browser cookies from exchange and wallet websites alongside Chrome saved passwords and iPhone text messages. With all of this information, the software can easily log into your account even bypassing SMS two-factor authentication.
Other malware may hijack your clipboard to replace a recipient wallet address with their own when you copy it over.
It’s essential that you have up-to-date antivirus software on your computer to protect yourself and your crypto from malware. Additionally, ensure that you’re always double-checking public addresses when sending cryptocurrency to another wallet.
9. Install Unknown Browser Plug-ins
Trustworthy crypto browser plug-ins such as MetaMask and Lolli can significantly improve your online experience. However, we can’t say the same for other extensions. The Internet is ripe with malicious plug-ins waiting to take advantage of victims who don’t understand what permissions they’re giving it.
For example, MyCrypto, a popular Ethereum wallet, reported on a plug-in that advertised five percent cash back on all blockchain transactions. However, the plug-in required write permissions for numerous exchanges and online wallets as well as access to your open tabs and cookies. After receiving these permissions, the plug-in could steal almost any credentials it wanted to.
Do intensive due diligence before installing a browser plug-in. Read reviews, scour Google for information, and make sure you understand exactly what permissions you’re giving the software. Stick with open-source extensions whenever possible.
Conclusion
Unlike banks with FDIC insurance, there’s no insurance for the loss of your cryptocurrency. If someone steals your crypto or you misplace the keys to access it, you’re out of luck.
There are a lot of pros to being your own bank with cryptocurrency, but those advantages come with an immense amount of responsibility. Take the time to put the proper security measures in place, so you don’t become the fool that parts with his (or her) crypto through avoidable mistakes.
Interested in learning more? Check out our 2018 Blockchain Security Threat Report.

